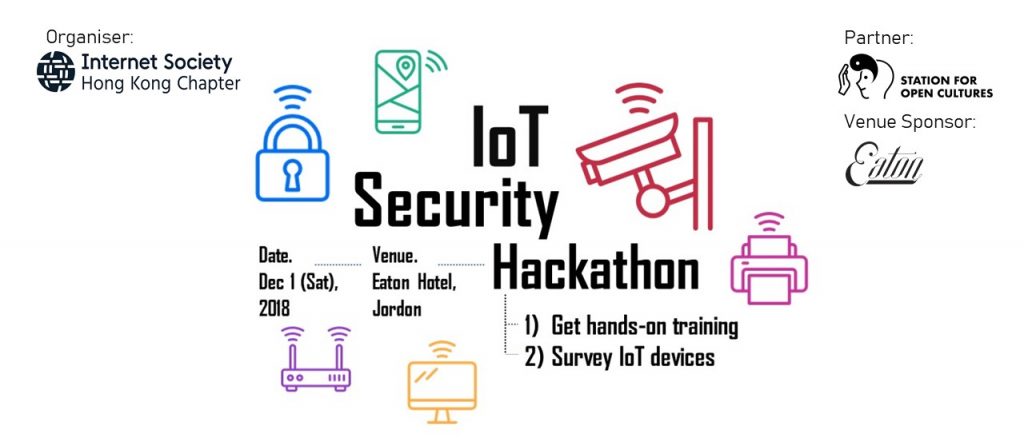
Event details:
Date: Dec 1 (Sat), 2018
Time: 10:00 – 18:00
Venue: 1/F, Eaton Hotel, 380 Nathan Road, Jordan
Fee: Free of charge; free snacks and beverage will be provided during lunch break
Language: Cantonese; materials in English
More information of the event: https://www.isoc.hk/news/iot-security-and-privacy-hackathon/
Workshop description and Speakers’ bio:
Introduction to IoT Security and Privacy Evaluation Project
Speaker: Charles Low and Edwin Chu
 Charles is one of the directors of Internet Society Hong Kong (ISOC HK) and he is currently a senior security consultant in NTT Security, specialising in threat and vulnerability management. He is experienced in IoT backend software development as well as security assessment on IoT devices.
Charles is one of the directors of Internet Society Hong Kong (ISOC HK) and he is currently a senior security consultant in NTT Security, specialising in threat and vulnerability management. He is experienced in IoT backend software development as well as security assessment on IoT devices.

Edwin Chu previously worked in Apple as Senior Software Engineer, specialising in planet-scale system and cryptography engineering. He is now the co-founder and CEO of a Hong Kong-based stealth mode tech startup which endeavours to solve security challenges in cryptocurrency industry.
Introduction to IoT Protocols and Security Testing
Many IoT devices use standard protocols to communicate. This elementary level session introduces the basics of common protocols used to help participants understand the languages of IoT devices. Hands-on exercises are also included to enable the participants to set up their own tiny security testing lab to sniff, capture, intercept and analyze traffic of IoT devices.
Speaker: Kenneth Tse

Kenneth is a senior consultant at a local security consulting firm with over 10 years of hands-on experiences in information security. He leads a team of ethical hackers to conduct penetration tests and simulation of attacks for customers from various industries. Being a security geek, Kenneth enjoys jamming with his geeky friends to research on security topics and hacking (legitimately) for fun.
Security Vulnerabilities of IoT Devices
The workshops goes in-depth into the security vulnerabilities of IoT devices through sharing of industry insights and technical details.
The demands of cut-throat competition, together with the end-to-end nature of IoT and the fact that all ODMs are located in China, have given rise to the Brands-ODM-SoC ecosystem for low cost and quick turnaround mobile devices. On top of this, there are only a small handful of SoC solutions for each type of IoT device, which are available on the Internet. Anyone with a little bit of technical background and persistence can do some digging and easily access different kinds of IoT devices. We are going to show you how easy it is to utilize the tools and concepts from the previous session to hack into everyday wearable devices.
Speaker: Wai Kong Sung
 Wai Kong Sung is currently a software consultant for an end-to-end Internet of Thing(IoT) solutions provider. In 2008, he co-founded one of the earliest Android start-ups which was later acquired by one of the major ODMs in China. Prior to this, he led the fixed-mobile convergence team in a Linux smartphone start-up which was a pioneer of baseband SoC design. He has also worked on embedded system software and operation support systems (OSS) for telecom carriers in the United States.
Wai Kong Sung is currently a software consultant for an end-to-end Internet of Thing(IoT) solutions provider. In 2008, he co-founded one of the earliest Android start-ups which was later acquired by one of the major ODMs in China. Prior to this, he led the fixed-mobile convergence team in a Linux smartphone start-up which was a pioneer of baseband SoC design. He has also worked on embedded system software and operation support systems (OSS) for telecom carriers in the United States.
Static Analysis of Firmware and Walkthrough of how a Router Expliot is discovered
This workshop introduces firmware analysis, methodologies to retrieve firmware and static analysis of firmware with two case studies of two brands of router.
Speaker: Chris Chan
 Chris Chan is a security analyst of UDomain Web Hosting Ltd, focusing on web application security, malware analysis and various research. He contributed to malware analysis for a Hong Kong Threat intelligence sharing platform and first CTF in Hong Kong. With the malware analysis skill he helps company detect attack on client. He holds OSCP,OSCE and CEH and is providing penetration test for web hosting clients. He was a speaker of security congress APAC 2017 and DragonCon 2017.
Chris Chan is a security analyst of UDomain Web Hosting Ltd, focusing on web application security, malware analysis and various research. He contributed to malware analysis for a Hong Kong Threat intelligence sharing platform and first CTF in Hong Kong. With the malware analysis skill he helps company detect attack on client. He holds OSCP,OSCE and CEH and is providing penetration test for web hosting clients. He was a speaker of security congress APAC 2017 and DragonCon 2017.
Introduction to Bruteforce Technique
This workshop includes retrace of the history and implementation of passwords in our everyday applications. It highlights the flaws and attacks that allow us to crack passwords strategically. By the end of the session you will be able to conduct your own password attacks.
*This workshop will be conducted in English.
Speaker: Philip Mok
 Philip Mok is a Senior Security Consultant at NTT. He specialises in penetration testing with interests in OSINT, SOCMINT, and Red Teaming. He currently holds OSCP, OSCE, OSWP, CRT, and GWAPT. Philip is also a co-founding member of a networking group for penetration testers, “Hong Kong Cyber Security Professionals”.
Philip Mok is a Senior Security Consultant at NTT. He specialises in penetration testing with interests in OSINT, SOCMINT, and Red Teaming. He currently holds OSCP, OSCE, OSWP, CRT, and GWAPT. Philip is also a co-founding member of a networking group for penetration testers, “Hong Kong Cyber Security Professionals”.
Registration:
Registration form: https://goo.gl/forms/QV2sp2hF9IoqZ2m73
Deadline of registration: Nov 14 (Wed), 2018